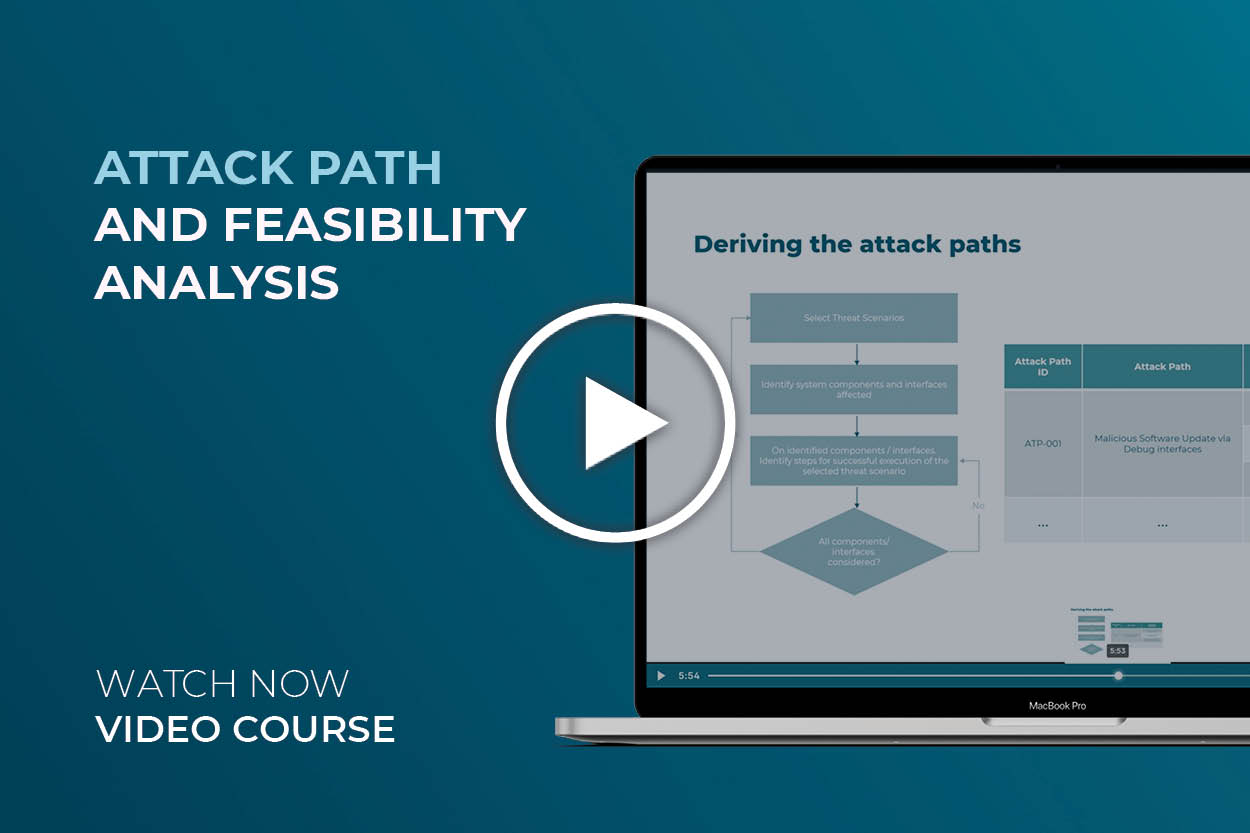
Attack Path and Feasibility Analysis – Video course
In this video course, you will not only learn what the attack path and feasibility analysis are, but also understand how each are done based on best practices. For instance, you will learn how to perform an attack path analysis using the recommended top down approach using the linear attack path structure. Additionally, you will learn how to calculate attack feasibility values.
Perform the attack path analysis and feasibility analysis based on best practices and in a systematic way
After the threat analysis and defining the resulting threat scenarios, we need to know how likely it is for a threat scenario to be realized by an attack. This is why the Attack Path and Feasibility Analysis must be performed as part of the TARA. In this video course, we will precisely explain both analyses, taking ISO/SAE 21434 requirements into consideration.
First, we will take a look at where the attack path and feasibility analysis are located in the overall TARA process and how they are used as input for the following activity, risk determination.
Right after, you will get an overview of the top down and bottom up approaches for the attack path analysis, as well as a visual clarification of how threat scenarios previously defined during the threat analysis are included here.
Once you understand how the top down approach works, you will get an explanation of the recommended by best practices linear attack path structure, as defining the structure is the next step in the attack path analysis. In a visual example, you will get to know how the threat scenarios and attack paths for each are presented based on this structure. Moreover, you will also get a visual overview on how to identify all attacks for each threat scenario in a systematic way to define the belonging descriptions.
As far as the feasibility assessment, we will explain what the process entails and which attack feasibility rating schemes are recommended by ISO/SAE 21434. Moreover, you will also learn which are the parameters for feasibility assessment and their corresponding levels. Finally, you will learn how feasibility calculations are done by taking the levels and values into account in a visual example.
Who the “Attack Path and Feasibility Analysis” video course is made for:
For system engineers
In this video course, you will learn how to improve the security of your system by performing a path analysis that provides you with more information about potential attacks and uncovering the potential vulnerabilities in the system.
For software engineers
Just as relevant for system engineers, knowing how likely an attack can be realized, is important to enable better security measures across systems. Especially, when cybersecurity measures are yet to be determined.
Attack Path and Feasibility Analysis – Video course content
Here, we will list the learning objectives of this video course and why they are important for your role and ISO/SAE 21434 compliance.
II. ISO/SAE 21434 Risk Assessment Process
Understand where the attack path analysis and attack feasibility takes place in the TARA, how it derives from the threat analysis and why it is necessary for further activities.
III. Attack Path Analysis
Understand the main two approaches to derive attacks, including the top down approach and the bottom up approach and how the resulting threat scenarios from the threat analysis are involved in a visual overview. You will also get use recommendations for both.
IV. Choosing a structural approach to attack path analysis
Since the ISO/SAE 21434 does not clarify how to implement a top down attack path analysis (the favorable approach), we will recommend and explain the linear attack path structure and show you how the end result looks like considering threat scenarios and attack paths.
V. Deriving the attack paths
Get a visual overview of the actions to perform to identify all attacks targeting each of the previously defined threat scenarios, and how attack paths and belonging descriptions are derived from here. An example is included.
Learn what the attack feasibility assessment process is, how together with the impact assessment serves for risks determination and what some ISO/SAE 21434 recommendations for attack feasibility rating schemes are.
VII. Attack potential factors
In this section, we will introduce and thoroughly explain the five parameters used for feasibility assessment and their corresponding possible levels or enumerates.
VIII. Deriving feasibilities
Understand how feasibility calculations are done by taking into account the previous parameter’s enumerate and assigning values. An example of the calculation is included.
IX. Lessons learned on Attack Path and Feasibility Analysis video course
Here, you will get a summary of the main takeaways from this video course