Home ▸ Automotive Cybersecurity Online Courses ▸ 04 Cybersecurity Management ▸ Vulnerability Analysis for Vehicle Cybersecurity
Understand vulnerability analysis in the context of continual cybersecurity activities, steps involved, and what the ISO/SAE 21434 demands
Get to know what the cybersecurity vulnerability analysis and role in continual cybersecurity activities is in this video course. You will also learn about what determines the treatment of a vulnerability and further steps as demanded by the ISO/SAE 21434. Most importantly, we will give you an overview of the steps in vulnerability analysis.
Watch video course
Discovering a weakness is certainly not desirable, but also you can’t stay with arms crossed. There is, of course, a standard required solution to handle cybersecurity weaknesses identified during the continual cybersecurity activities process. This is where the vulnerability analysis comes into play. In this video course, you will learn about what is the vulnerability analysis, necessary steps and decision making to treat vulnerabilities.
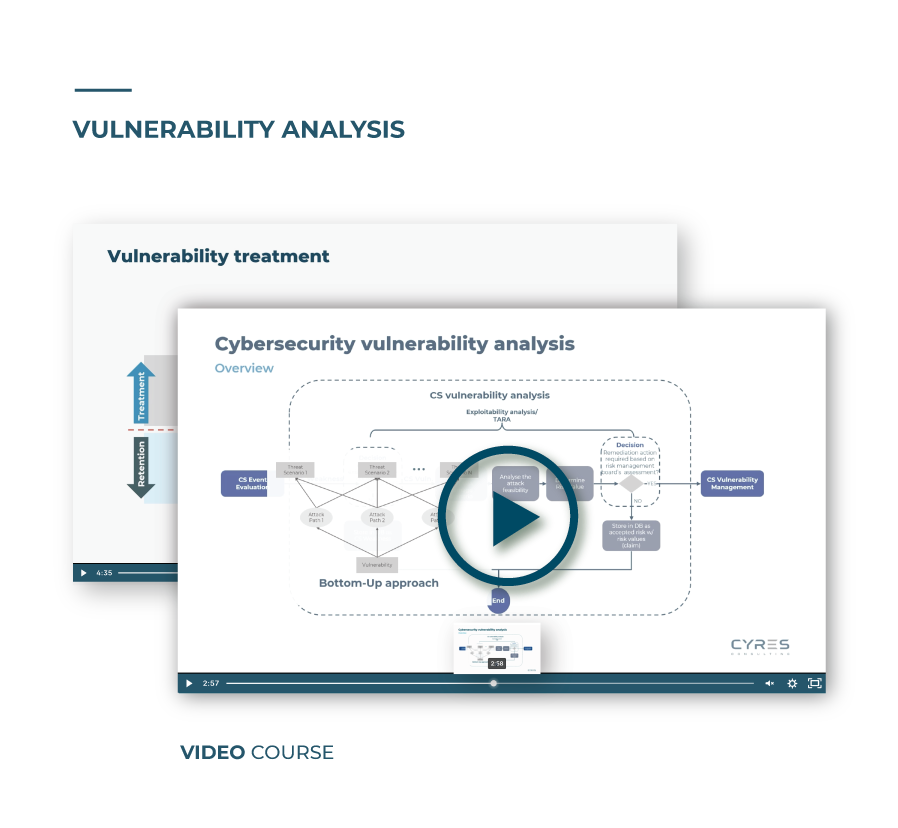
First, we will recapitulate on what continual cybersecurity activities are according to ISO/SAE 21434 and what the process looks like to afterwards give you an overview of what the cybersecurity vulnerability is. We will also introduce the concept of the exploitability analysis, which is the main activity taking place during the vulnerability analysis.
Next, we will provide an overview and the step-by-step process of the vulnerability analysis, which ultimately leads to deciding on further remediation action. Over this course, we will also explain the bottom down approach and top down approach and clarify where they need to be used.
At last, we will explain how the decision to handle a vulnerability is made and the further steps needed as required by ISO/SAE 21434 for both if further treatment is required and if no additional processing is required.
For quality managers
The vulnerability analysis plays a crucial role to keep a product secure throughout the entire vehicle product lifecycle. Therefore, this video course is important to get a whole picture on what needs to be done if weaknesses that compromise overall cybersecurity and, therefore, quality, are detected.
For system engineers
Being able to handle cybersecurity weaknesses with an effective and standard required solution, such as the cybersecurity vulnerability analysis is essential to correctly handle vulnerabilities. In this course, you will learn what steps are required and how to correctly decide how vulnerabilities should be treated.
I. Intro to Vulnerability Analysis
Understand what continual cybersecurity activities are according to ISO/SAE 21434 and the role of vulnerability analysis, the main activities taking place such as the exploitability analysis, and its purpose.
II. Cybersecurity Vulnerability Analysis
In this section, we will explain the exploitability analysis into more detail. You will also learn how the approach from determining attack paths differentiate from the TARA and the steps along the vulnerability analysis.
III. Vulnerability Treatment
Here, you will learn about the decision making involved on how to handle the vulnerability, what determines the decision, and what the ISO/SAE 21434 requires if no additional processing is needed.
IV. Vulnerability analysis final thoughts
Finally, we will summarize what you have learned during the video course.
Cybersecurity requirements for post-development are demanded by UN R155 and ISO/SAE 21434:2021. Learn the main considerations in this video course.
Know what the pre-requirements and specific contents of the Production Control Plan are. Learn about this major work product with this video course.
Learn about the release for post development report as a work product for ISO/SAE 21434:2021 and UN Regulation No. 155. Watch video course.
In this video course, you will learn about how to approach communication and stakeholder management in vehicle cybersecurity as required by ISO/SAE 21434:2021.
Understand what cybersecurity monitoring and event evaluation is based in the cybersecurity continual activities framework. Watch video course.
In this video course, you will learn exactly all the Product Security Incident Response Team or PSIRT service areas, their purpose, and contents.
Learn what a cybersecurity incident response plan is and what it should contain to comply with ISO/SAE 21434 in this video course.
Learn what is the cybersecurity vulnerability analysis in continual cybersecurity activities and as required by the ISO/SAE 21434. Also, learn how to correctly decide a course of action to treat a vulnerability.
Learn how to create a cybersecurity case, which is a work product of ISO/SAE 21434. In this video course, you will also get lessons learned from real projects.
Learn about the supplier selection process in automotive and which cybersecurity capabilities should be followed to comply with ISO/SAE 21434 and other automotive cybersecurity standards and regulations.
Learn how to build the structure of the Cybersecurity Interface Agreement as required by ISO/SAE 21434. Template incl. in this 7 min video course.
Learn what is a cybersecurity plan in automotive and what aspects are required by ISO/SAE 21434 in this short video course and sample plan.
Understand why tool management is crucial and what is required from the ISO/SAE 21434 standpoint, while taking ISO 26262 as a base to define the tool management methods.
Get an overview on managing cybersecurity at the organizational level as for ISO/SAE 21434 and required work products. Watch video course.
Learn more about automotive cybersecurity audits and assessments in this video course. Get a glimpse on how ISO/PAS 5112, ASPICE, VDA QMC ACSMS can support you to audit and assess along the ISO/SAE 21434 and UN R155.
Learn how competence management according to ISO/SAE 21434 can be achieved and recognize the negative consequences of ignoring it.
The cybersecurity policy is a requirement for ISO/SAE 21434 and UN Regulation No 155. Learn about it on this video course.
Building cybersecurity culture is a requirement for ISO/SAE 21434 and an important component that benefits organizations.
Learn how to manage and plan cybersecurity in the project lifecycle and understand the possible negative consequences if ignored.
Learn how distributed development enables successful projects in automotive and meet ISO/SAE 21434 expectations.
In this video you will learn how important is to include Cybersecurity in Project Management activities to ensure project success.
Cybersecurity Planning is crucial for ISO/SAE 21434. Get guidance on structuring a cybersecurity plan and cybersecurity case on this video course.