UN Regulation No. 155 is increasing the pressure on the automotive industry to address cybersecurity. The industry is taking action: New resources are being allocated to the topic, responsibilities are being assigned, and specialists are urgently sought everywhere. At present, their main task is to provide truly reliable answers. For example, on the question: What does UN Regulation No. 155 require of actors in the automotive industry?
- I. A short overview: Background knowledge on UN Regulation No. 155
- II. How are the UN Regulation No. 155 and ISO/SAE 21434 related?
- III. What are the UN R155 requirements?
- IV. When is the UN R155 coming into effect?
- V. UN R155, USA, China, “Self-Declaration” and GTRs
- VI. Is the UN R155 only relevant for OEMs?
- VII. Achieve compliance with UN R155: How to implement a Cyber Security Management System?
- VIII. Do your current processes, as they are, comply with UN Regulation No. 155?
- IX. A lot of groundwork for one purpose: Ensuring type approval before SOP
There is no way around systematically dealing with UN Regulation No. 155 in the entire automotive value chain in order to be able to do business and be competitive. Cybersecurity in product development is becoming a key factor for the success of the entire organization.
The good news here is that in very few cases do processes, methods and the entire organization start from scratch when it comes to applied automotive cybersecurity in accordance with UN R155. Therefore, the most important question to start with is: What is your own organization’s status quo concerning the given level of compliance?
In order to get answers as quickly as possible, experience has shown that in practice we advise taking the following first two steps:
- Create awareness of the fundamental principles of automotive cybersecurity at the executive and management levels, as well as within ongoing project activities.
- Initiate a valid assessment at an early stage between the regulatory requirements and the procedures in place in the organization, the application in practice and the efficient reuse in the projects.
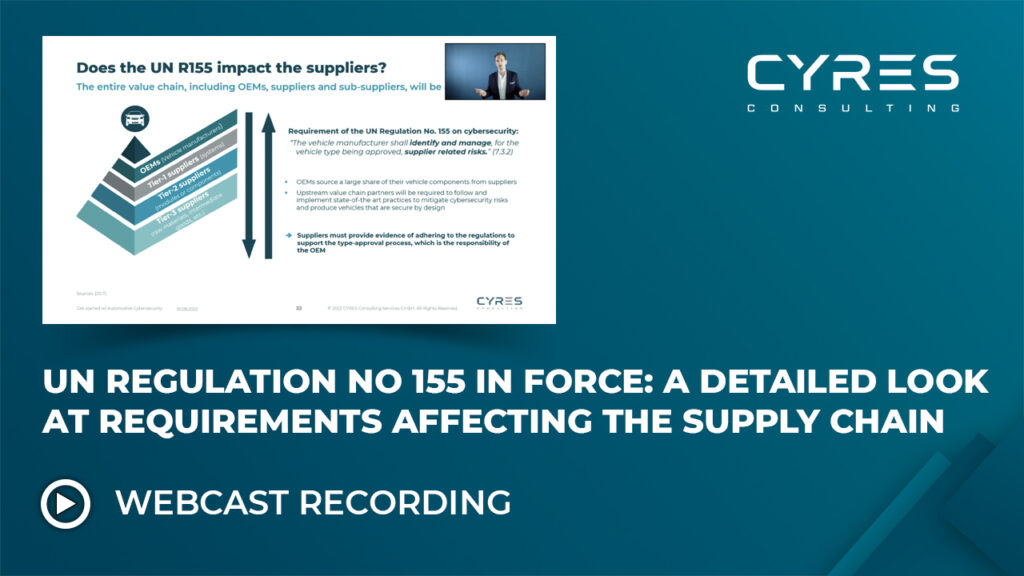
- Watch full recorded webcast “UN Regulation No. 155 is in force: A detailed look at requirements affecting the supply chain”
A short overview: Background knowledge on UN Regulation No. 155
Originally founded as the Working Party on the Construction of Vehicles, UNECE WP.29 is the world forum for the harmonization of vehicle regulations of the United Nations Economic Commission for Europe. What is set up here is to be regarded as the “UN regulations” for international vehicle construction.
The UNECE WP.29 deals with the harmonization of vehicle regulations for vehicles and vehicle equipment. One of the most important recent regulations is the UNECE Regulation No 155 concerning the approval of vehicles with regards to cybersecurity and Cyber Security Management System.
Within the WP.29 there are six permanent working parties, which deal with specific topics around the vehicle. The GRVA is one of these working parties and deals with automated and connected vehicles. This working party is also the starting point for the UN R155 as well as for the UN Regulation No. 156 (for more information see our topic page UN Regulation No 156 & SUMS).
So, UNECE WP.29 GRVA specifies in UN Regulation No. 155 (UN R155 for short) specific requirements for cybersecurity and for the so-called Cybersecurity Management System (CSMS). Although UN R155 is already very comprehensive, there is no way around the associated consideration of ISO/SAE 21434 (see also our recent blog on the official publication of ISO/SAE 21434:2021).
Now the question arises, what the current situation regarding the overall interrelationships between ISO/SAE 21434 as a standard in relation to UNECE Regulation No. 155 looks like.
First and foremost, it is important to distinguish the terms standards and regulations.
Standards are usually reference points designed by the industry itself under the control of an authority such as the ISO (the International Standards Organization).
Standards are considered to be state-of-the-art references. For example, ISO/SAE 21434 Road vehicles – Cybersecurity engineering provides the framework for requirements and recommendations to develop a cybersecure product in the automotive industry. ISO/SAE 21434 does not offer any fixed suggestions for solutions, but only a purposely abstract framework.
In simple terms, the evidence that one has worked along a standard could be used in court to verify whether something is developed according to the industry standard and way of working, just by using an ISO standard as a reference.
Regulations, in contrast, are legally binding directives issued by an official body, such as a government.
In the case of the automotive industry and the UNECE Regulation No 155, these are binding requirements that must be complied with in order to obtain type approval and therefore market access. A lack of compliance with the regulation can consequently lead to a sales ban in the corresponding area of application (in case of UNR 155 over 60 countries already are adopting the regulation).
These regulations often use the standards to have a thematic point of reference.
Here, the UNECE refers to the ISO/SAE 21434 Road Vehicles – Cybersecurity Engineering standard. This was made especially clear in the published interpretation document of late 2020, which related the requirements of the regulation to the various requirements of ISO/SAE 21434.
In other words, the ISO 21434 industry standard provides support for meeting the requirements of UNECE Regulation No. 155.
(To draw a parallel from information security: Here the implementation of the ISO 27k-series would be one thing, the EU GDPR/DSGVO as applicable law, the other).
Watch our UNECE 155 video course for more details:
What are the UN R155 requirements?
Different than ISO/SAE 21434, which does not explicitly specify particular processes (but requires compliance and the establishment of work products to ensure compliance), UN R155 requires the setup and implementation of a management system that focuses on cybersecurity along the vehicle (the so called Cybersecurity Management System or short CSMS). You can also read our article on how to establish a Cybersecurity Management System CSMS.
The Cyber Security Management System is of central importance for ensuring the cybersecure organization in the automotive industry. Moreover, the CSMS provides basis for the Certificate of Compliance for CSMS, i.e. the auditing and the corresponding official certification.
For this purpose, the VDA (the German Association of the Automotive Industry) has released a questionnaire (still in draft status, finalization is still pending; The Red Book will be released soon), which is intended to provide an initial basis for the audit protocol as a rudimentary checklist. Here, the requirements are taken and reformulated into questions or scenarios on how to cover the requirements for CSMS.
How is auditing carried out in accordance with UNECE Regulation No. 155? Two entities are relevant here. Firstly, the official approval authority (such as the Federal Motor Transport Authority under the Federal Ministry of Transport and Digital Infrastructure), and secondly, an institution at the technical level.
Moreover, companies are becoming aware that ISO/SAE 21434 is not only about the product, but also about projects and the entire organization. Similarly, the UN R155 covers not only the product but also product development and the organization.
On the one hand, UN R155 is about ensuring cybersecurity at the organizational level. The objective here: ensuring cybersecurity principles are implemented in core of the business and its processes.
On the other hand, it is all about the product and type approvals. The objective here: ensuring the design of the vehicle architecture, risk assessment and implementation of adequate security controls.
What is demanded by UN R155 is strongly based on the requirements of ISO/SAE 21434, which is why ISO/SAE 21434 helps in the creation of processes for the CSMS, as well as for ensuring type approval.
When is the UN R155 coming into effect?
The UN Regulation No. 155 came into force at the beginning of 2021, and two dates are binding: from July 2022, the requirements within the UNECE member countries (from the 1958 Agreement) will apply to all new vehicle types for type approval, and from July 2024 they will apply to all vehicles.
It is important to know that UN R155 is binding for type approval in the now 64 member countries. These (initially 54 and since 2022) 64 member countries are based on the 1958 UNECE Member States Agreement (see also here).
Although the USA and China, for example, do not belong to the UNECE’s area of application, experts believe that UN Regulation No. 155 will develop into a “de facto global standard”.
The main reason for this is that vehicle approval in the USA is not synonymous with approval in the member countries. This means that vehicles authorized for use in the USA cannot be brought onto the global market or the market of the UNECE member countries on the basis of this approval.
UN R155, USA, China, “Self-Declaration” and GTRs
For this reason, there is the possibility of a so-called “self-declaration” for non-UNECE member countries. This is already being realized in the USA and Canada. Requirements on the basis of UN R155 are defined by the local authorities; for the USA, for example, this is the U.S. Fedaral Motor Vehicle Safety Standards (FMVSS).
The OEM must meet these requirements accordingly and declare its conformity.
In general, market entry is possible without a type approval along a certain regulation, such as the UN R155. After market entry, however, the Approval Authority of the respective country reserves the right to carry out compliance tests in order to recall the vehicle in the event of possible non-compliance.
You can also watch this short video course to learn more about the Authorities and Institutions for Automotive Cybersecurity.
China is also officially outside the area of application of UN R155. However, OEMs here must ensure similar requirements for type approval (the so-called CCC “China Compulsory Certificate”) and even cover local-specific aspects from the China Cybersecurity Law.
For countries that do not belong to the scope of the 1958 Agreement (see above), such as countries included in the 1998 Agreement, it might become possible to implement the requirements specified in the scope of the 1958 Agreement through so-called GTRs (global technical regulations).
Since 1998, several GTRs have already been published (e.g. for pedestrian safety as well as regulations concerning hydrogen and fuel cell vehicles). Therefore, it is thinkable that the UN R155 will be treated accordingly, which could simplify a homogenization with countries which do not belong to the UNECE Member Countries along the 1958 Agreement. However, type approval requirements are not in scope of the 1998 Agreements and its GTRs.
Is the UN R155 only relevant for OEMs?
We have already learned that an important aspect of UN Regulation No. 155 is the introduction of a certified Cybersecurity Management System as part of the consideration of cybersecurity aspects in the type approval process. Can we therefore conclude that UN R155 is actually only an issue for OEMs?
The OEMs must demonstrate that the CSMS is managed along the entire value chain and are accountable for it. Consequently, all players involved need to be aware of potential risks and gaps, from Tier 1 till Tier n supplier level. This means that suppliers must also work in compliance with the CSMS principles.
Moreover, an audit or the Certificate of Compliance for CSMS is required and must be obtained at least every three years. To build a link to type approval: This CSMS certification is the prerequisite for type approval in the first place. Then there are the additional detailed requirements relating to the product. As creation and implementation of new organization wide rules and processes can be painfully slow, it is advisable to take the necessary steps at an early stage.
Since a considerable proportion of cybersecurity-relevant components of the vehicle still come via suppliers, it becomes obvious very quickly that they are widely involved in the multidimensional requirements of UN R155.
On the one hand, because it is necessary purely in terms of a vehicle’s structure, and on the other hand, because OEMs are also obliged to efficiently address this resource-intensive complexity.
For example, consideration of the UN R155 requirements is already today part of the Statements of Work of well-known OEMs.
Achieve compliance with UN R155: How to implement a Cyber Security Management System?
What sounds like a simple question to which Google could provide a quick answer is a multidimensional and far-reaching undertaking that involves the entire organization as well as technical details of the product along the entire lifecycle at several levels.
At the same time, the question doesn’t really arise like this, because – fortunately – in terms of cybersecurity requirements, an organization usually doesn’t start completely from scratch.
It is therefore a matter of reviewing the organization’s own status and its own processes in order to be able to determine the correct consideration of the requirements in a holistic manner.
At this point, based on our experience (regardless of organizational structure and size of the enterprise), we have to state: Please be sure to plan for sufficient staff, resources and, above all, time to be able to handle this extremely demanding task. Unfortunately, we repeatedly receive inquiries based on unrealistic assumptions.
The CSMS is the benchmark and starting point for type approval. Accordingly, in practice, this is where the main attention is paid. Without the corresponding Certificate of Compliance for the CSMS, the actual type approval cannot even be initiated.
Do your current processes, as they are, comply with UN Regulation No. 155?
In order to develop valid answers to the above question, the following procedure is recommended in practice:
1. Define scope, analyze and define action plan
It is important to understand the current cybersecurity processes as comprehensively as possible. For this, it is helpful to perform a gap analysis (see our ISO/SAE 21434 Gap Analysis). Especially if ISO/SAE 21434 principles are already established in the organization.
Based on these gaps, action items can be derived and topics or processes that are necessary for a CSMS can be broken down in a structured manner. Creating an overview is elementary.
2. Implementation of the framework
During implementation, it is important that there is a general understanding and awareness of automotive cybersecurity within the organization.
This ensures that processes are rolled out holistically and that a continuous improvement process is in place.
Also, any deviation from the state of the art should be recognized at an early stage by each process participant in order to initiate measures early enough to ensure a direct counteraction.
This is an essential prerequisite for piloting the CSMS.
3. Piloting, ongoing alignment + certification
Once the processes have been implemented, the pilot phase follows. Lessons learned and sanity checks are essential. Continuous monitoring of the processes is also directly required by UN R155.
Internal audits are helpful in preparing for the actual certification by Technical Services.
It is important here to consistently follow the relevant timeline. Type approval should be available at the start of production (SOP). Type approval can take up to three months. Before the actual type approval, the CoC for the CSMS must be available. You should also plan a processing time (incl. audit) of three months for this in any case.
Simple mathematics: This means that a CSMS must be in place six months before the actual SOP.
The implementation of the CSMS is strongly based on the given processes around cybersecurity as well as the already given compliance with the ISO/SAE 21434 standard.
A lot of groundwork for one purpose: Ensuring type approval before SOP
As mentioned, without CSMS (and the associated Certificate of Compliance), type approval is not possible.
The result of this is an inability to enter the market, leading to a significant competitive disadvantage for OEMs.
It is important to mention here again that UN R155 is nevertheless not a subject purely for the OEM. Tier-N suppliers also need to ensure that cybersecurity principles are systematically embedded in their organizations.
In our consulting experience, we see that the associated requirements are already pretty much part of the daily business and therefore already represent an important Supplier Selection Criteria.
To sum it up: The sooner OEMs and especially Tier-N suppliers (who are always at risk of approaching this too late) address the issue of CSMS the better. Cybersecurity requirements are to be seen here as a pure time issue: The earlier a systematic approach is taken, the fewer issues will occur later in the rollout or audit.

Manuel Sandler has many years of experience in global project and process management in various parts of the value chain, including OEMs and Tier-1. He is ASPICE Provisional Assessor and an expert in Engineering Process Development, ISO 26262, ISO/IEC 15288 and ISO/SAE 21434 Road Vehicles – Cybersecurity Engineering.







Comments are closed.